What is Proxy server?
A proxy server is an interface server between the servers and the source and destination client. This server acts as a gateway between the Internet and the user.
Proxy Server offers different levels of security, performance, and privacy depending on the needs and types of user usage.
How does Proxy Server work?
When a client sends a request, The proxy server checks this request then sends it to the Internet environment and passes it through the firewall.
After receiving a response from the destination client, it checks it again to send, and finally, the response is sent back to the source server.
When a request is sent from you to the web, it first goes through the Proxy server filter and sends it to the web server.
The Proxy server collects the response from the web server and sends the data from the web to your source system so that you can reach the answer in your system browser.
The proxy server can change your IP so that the web server cannot detect your location correctly.
It also encrypts information to protect your data in the submission process from being readable and can block access to some web pages based on IP address.
5 Mainly Reasons to Use a Proxy Server
Organizations and individuals use Proxy Server for different purposes and functions to use proxy server advantages:
-
Privacy
The proxy servers can change IPs, and some of them recognize information related to web requests.
Using a proxy enables users to hide the personal information of individuals and information displayed by searched websites.
-
Advanced security
Individuals and organizations can pair the proxy server with a virtual private network and access the Internet directly through a remote proxy server.
Organizations can also monitor the access of these users to the resources they need, such as email or internal information.
-
Proper speed and bandwidth
If thousands of people want to visit a site simultaneously, the Proxy server sends only one request to that IP Address to prevent bandwidth reduction.
By caching popular sites and information, the answer to the request is quickly provided to the user from the cached data, which will have a quick response and save bandwidth.
-
Restrict users and control Internet usage
Organizations can monitor how employees use the Internet and all web requests, which determines how much time employees spend in cyberspace.
They can even set restrictions to prevent employees from accessing websites designated by the organization.
-
Access to blocked resources
A proxy server can provide access to resources that are restricted or blocked by the organization or government by changing the IP and using the IPs of other countries.
Types of proxy servers
Proxy servers have different types based on performance and efficiency. You should use them according to your purpose.
-
Transparent Proxy
It provides the user’s original IP Address to the site, introducing the user to the web server, and it has elementary settings.
Commonly used in schools and public libraries to filter content.
-
Anonymous Proxy
This type of proxy server specifies its identity for the website but protects the identity of the user and information related to the user’s browsing history.
It prevents the transfer of the user’s original IP address to the website. One of the advantages is the display of websites that are relevant to your location.
-
Distorting proxy
This type also introduces itself as a Proxy server.
It does not provide the correct IP address to your website and uses the IP of other areas, which can also be beneficial for users.
-
High Anonymity proxy
A high Anonymity proxy is the most private and secure method.
It does not introduce itself as a proxy server and regularly provides different IP addresses to web servers.
As a result, it is impossible to identify which traffic is related to which system.
-
Data Center Proxy Server
This type of Proxy is not affiliated with the ISP Internet Service Provider and keeps users’ identities hidden on the Internet by creating fake addresses.
They are cheaper and faster than residential proxies, but they face more problems, such as blocking their access to some websites and making them easier to identify.
-
Residential Proxy Server
Residential Proxy Server Provides real IP addresses from a physical location to users and is dependent on ISPs.
Although they are more expensive than Data Center Proxy Servers, they are reliable because of the use of actual IP addresses in terms of web servers.
-
Mobile Proxy Server
This type of Proxy uses the IP addresses of devices that have mobile data, tablets, and smart devices.
Mobile Proxy Server is commonly used to test advertisements and applications, product development goals, and UX.
Protocols of Proxy Servers
-
HTTP Proxy
A common proxy that is based on the HTTP protocol and also supports the FTP protocol and is designed to use the content of websites.
-
HTTPS Proxy
This type of proxy using the HTTPS protocol is more secure than HTTP and uses port 443.
Usually, this type of proxy is used by hackers for intrusion and attacks such as Brute Force.
-
FTP Proxy
FTP Proxy with FTP protocol is designed to transfer files over the network.
It limits the time of access and access restrictions from external and internal networks and uses port 21.
-
SMTP Proxy
The SMTP protocol is used to send and receive emails.
It is used to determine the size and number of messages, filter the executive content of emails, and access email addresses.
Some hackers use this proxy to send spam messages to emails.
-
Forward Proxy
It receives data from groups of users in the internal network by sending a request to the proxy server to check whether it continues to establish a connection or not.
The possibility of administrative controls is provided most simply, and the security of IP addresses of individuals in the network is provided.
-
SSL Proxy
This proxy type is effective for organizations that need more protection against threats.
Also, if an SSL Proxy is used in connection with a website, because of Google’s attention to SSL, it impacts the site’s search engine rankings.
Proxy Server Lists
-
Public Proxy Server
This type of Proxy server is known as Public Proxy Server, open Proxy, or shared Proxy because it is free and available to all users.
Users can use it to operate anonymously on the Internet.
It is ideal for those who do not want to pay but has security and speed issues that are a major concern for many users as their sensitive data is compromised.
-
Private Proxy Server
Provides users with exclusive access to the IP Address and has excellent security due to the unique IP Address belonging to each specific user.
It is a good option for those whose security is the most important factor and for those who can afford to pay for these services.
Proxy server applications
Let’s check the benefits of proxy server:
- Bypass restrictions and blocked resources.
- Monitoring and controlling the browsing history of users and the activities of specific users in the Internet space.
- Bypass firewalls.
- Increase security by encrypting and hiding IP Address.
- Increase download speed.
Proxy Server risks
It is better to be aware of the common dangers of Proxy servers and be careful not to encounter any problems:
- Risks of Free Proxy Servers: You are recommended to not use free proxies to protect your sensitive data since they allow other parties to monitor your traffic, using them is dangerous.
- History Danger: The Proxy server stores information about the user’s web requests by accessing the user’s original IP address. So, check whether the Proxy server stores this information or not.
- Risk of non-encryption: Without encryption, your requests will be sent as text and anyone with access to your username and password can abuse your information.
Proxy server security methods
- Filtering user requests
- recording all activities
- Checking the content of transit packages.
- Ability to identify users
- hiding the internal network structure from the view of external users in the Internet space.
- Checking the content of the package under the standards of the protocols.
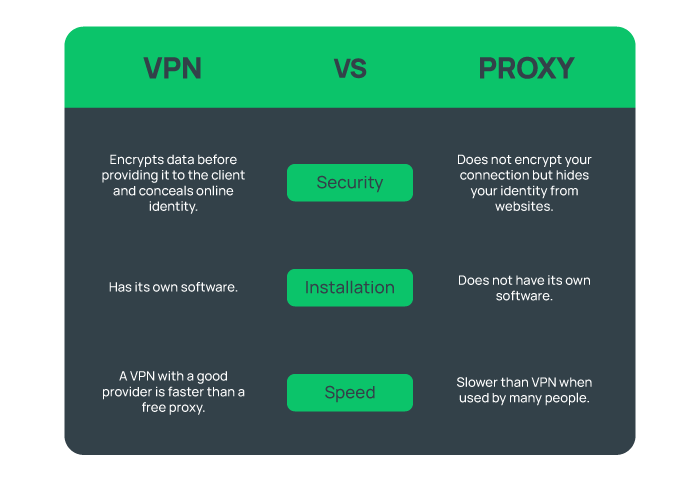
What are the differences between a VPN and a Proxy server?
VPN and Proxy servers try to protect the user’s connection information and location by changing the IP Address.
Despite these similarities, when it comes to Proxy vs VPS, there are fundamental differences in support for protocols and their Security function:
- VPN is configured at the system level and does not need to be configured separately. Proxy servers need to be configured separately.
- VPNs are more secure than proxy servers because VPNs create an encrypted tunnel between the user and the Internet network.
- A website cannot be hosted on a proxy server. With a VPS, you have more flexibility and customization choices; you may freely set up and run the server.
- When questioning VPS vs proxy, you need to know that your sensitive information cannot be concealed by proxy servers.
Proxy Server settings in Internet Explorer
- Install Internet Explorer software and then select Internet Options from the settings menu.
- After a window opens, select the Connections option in the top bar of the window and click on the LAN Setting option.
- Then, you will see the Local Area Network (LAN) settings page:
- If your network is connected to a specific website, choose the Use Automatic Configuration Script option and enter the desired address.
- If the connection to the network is made through a special port and IP Address, Select the Use a Proxy Server for Your LAN option and enter the required information.
- If your company and organization have set up a private network, You connect to the network through the Bypass proxy server for the local address option.
Then click OK to save the changes.
Note: To disable the Proxy server, Uncheck Use a proxy server for your LAN and click OK.
How to set up a Proxy server?
Proxy server setup and settings are different on operating systems and browsers, but the main thing you need to do is set up a LAN on your web browser or operating system.
After setting up the LAN on the operating system or browser, enter the Proxy Server address, port number, and related information.
You have to make the settings according to your operating system:
- Setting up a proxy server in Windows and macOS is not complicated but requires guidance.
- On iOS, you need to go to WiFi settings to configure the Proxy.
- In Safari, you have to configure the Proxy server in the settings section of the Safari application system.
- In the Mozilla Firefox browser from its network settings section.
- In Google Chrome browser find the setting of a proxy server through Devices> Networks.
- If you are using the Linux operating system, you need to follow some required steps to setup Proxy settings on Ubuntu.
What is a proxy server used for?
The most important usage of a proxy server is keeping your system and data secure as a protective layer. To have a relay between users and the internet, a proxy server is required.
One of the advantages of proxy server is that it helps to hide your IP address and in conclusion your location and identity.
If you need to bypass geographical restrictions on the internet, a proxy server is helpful. Also, it does not let cyber attackers enter your private network.
To control your employee’s access to your website, using a proxy server is a good idea. Since a proxy server helps to compress traffic, companies use it to save bandwidth.
Should I have a proxy server on?
Depending on your system security, you must have a proxy server on. It helps to improve system performance and use websites anonymously.
Parents and schools can use proxy servers to control the content children access.
Other reasons you can consider are to save bandwidth, increase speed, bypass filters, and private streaming.
Proxy servers may hide your identity from websites, but they do not encrypt your connection.
Using a public proxy server results in a less secure connection than connecting to a web server through a browser.
VPNs are a secure solution because they encrypt data before sending it to the client, hiding your identity from the web and your ISP in the process.
Should I leave proxy on or off?
An on-proxy server increases data usage and decreases internet speed. So, if you need to use its advantages like being anonymous, it must be kept on.
Is a VPN a proxy?
A VPN is a type of proxy that provides privacy differently from proxies. While all proxy servers are not VPN servers, a VPN server can be thought of as a proxy server.
The main differences are:
- A proxy needs a configuration, but a VPN protects the internet connection.
- VPNs come with an additional layer of security and protect your data perfectly.
- Proxies use HTTPS to secure your connection, which is not that much safer.
How do I find my proxy server address?
Finding the address of your proxy server on different operating systems and browsers requires a specific method.
For example, on Windows, you must follow the below path:
- To launch the Run dialog box, use the Windows key + R.
- Press Enter after typing “inetcpl.cpl” to bring up the Internet Properties.
- Select the Connection tab.
- Select the LAN settings option.
- Select the option “Use a proxy server for your LAN.”
- Enter the address and port that your proxy server has supplied.
- To save the changes you made, click OK.
What are the risks of proxy servers?
Using a proxy server comes with some dangers such as:
- Security issues
- Lack of encryption
- Privacy concerns
- Open ports
- Variable speed
- Tracking
- Difficult configurations
- Costly setup and maintenance
- Virus attacks
- Limited bandwidth
Is it bad to disable proxy server?
Disabling the proxy might cause impaired network performance and slow internet browsing.
Also, users may no longer be able to access particular services or websites that are geographically limited.
So, you are recommended to not connect to websites without an intermediary server to be more vulnerable to online crimes like identity theft and hacking attempts.
But if some software applications/services are not compatible with the proxy servers, you can disable it to let the apps connect to the internet directly.
Does a proxy change your IP?
Yes. The proxy server changes your IP address and then connects you to your considered websites and online services.
During the connection, the websites and online resources can recognize the IP address of the proxy server but do not see your IP address.
Which is faster VPN or proxy?
Users might experience a higher speed with free and paid VPNs because of the ideal servers and good bandwidth.
On the other hand, free web proxies are very slow, but a good proxy can be faster than a VPN service since it does not encrypt data.
What is proxy in WIFI?
A WiFi proxy encrypts your internet traffic to keep your device and IP address anonymous.
It is used to be redirected to the websites through an intermediary server and improve security and privacy.
Proxy in WiFi secures your important data from cyber-attacks by preventing websites from tracking your online activities.
What is an example of a proxy address?
A typical proxy address format is “192.168.1.1:8080,” where “8080” is the port number and “192.168.1.1” indicates the IP address of the proxy.
Proxy addresses can have any combination of alphanumeric and numeric characters.
Proxy addresses safeguard your important data from being exposed to the internet.
Why is proxy illegal?
Depending on the proxy use case, it can be legal and illegal. For example:
- Competitive Sabotage
- Fraudulent Transactions
- Cyber Espionage
- Unauthorized Access
- Unethical Competitor Analysis
- Intellectual Property Theft
- Misleading Advertising
and more, are illegal use cases of proxies.
Why do hackers use proxy servers?
Since a proxy server enables users to change/hide their IP address and location, hackers find it a good way to do illegal online activities while their identity is hidden.
What is safer VPN or proxy?
VPN is safer and encrypts data.
While VPN providers host the network, they have control over users who access it, a proxy is not that safe because it acts only as a gateway.
Which proxy server is best?
The most reported as the best proxy servers are:
- Smartproxy
- Oxylabs
- Nimble
- Bright Data
- IPRoyal
- Squid
- Traefik
- NGINX
- SOAX
- Webshare
- MPP
- Proxy-seller
What is a proxy URL?
To access the server and enter the proxy server, the URL is required. It can read data and change the settings.
It is created by adding a target URL to the proxy prefix, enabling access via a web browser.
Does a proxy slow down Internet?
No. Proxy servers don’t always cause your internet speed to lag. Several factors affect the speed at which proxies function such as:
- Distance between you and a server.
- Rotation and Server Selection
- The internet speed of your ISP.
- The ISP of an IP that you are connected to.
- Proxy Provider’s Infrastructure.
The totality of these factors accounts for the pace you are experiencing, which may be lower than typical.
Is My internet Connection behind a proxy server?
You need to check it using different methods on Windows, Linux, and browsers.
Online Proxy detection tools can be helpful. A configured proxy server must be visible if you check your network settings.
Try connecting to a non-existent server. You may be using a proxy if the error that appears on the page doesn’t seem like the one that usually appears.
Can I use VPN and proxy together?
Yes, but not recommended because of slowing down the speed and extra costs.
The encryption between the VPN client and the VPN server causes the speed to decrease. So, you cannot expect the normal speed of the proxy.
If you need extra protection and a layer of security to your connection and system, you can use a VPN and a Proxy together.
Also, a VPN can keep your IP address hidden if your proxy fails.
Does Google have a proxy server?
No. Google doesn’t provide a dedicated proxy server service directly. Google Translate and Google Web Light can be used as a Proxy Server.
How do I use a proxy in my browser?
You can use proxy servers on your default browser. Here, we explain configuring proxy on Google Chrome:
- Open Chrome and select Settings from the three dots menu icon.
- Click “Change proxy settings” under the “Network” section.
- Check the box next to “Use a proxy server for your LAN” under “LAN Settings.”
- To establish a connection with a proxy server, provide its IP address and port number.
- To save the changes, click “OK.”
- Use the address bar to type a web URL to test the connection.
Can a proxy give you a virus?
Yes. Proxy servers have limited privacy.
Using free proxies is risky because they work on ad-based revenue models, which lets others listen to your traffic.
These advertisements frequently contain malware, such as viruses, that can quickly infect devices.
Why use proxy instead of firewall?
While firewalls protect your network from cyber threats and control traffic, you must use a proxy instead of a firewall if the below options are your priorities:
- Access content anonymously with a concealed identity.
- Improve privacy and performance.
- Access to geo-restricted websites.
Are proxy servers safe?
Proxy servers are not completely secure. A proxy server hides your IP address, online identity, and location.
But surfing the internet is not 100 % safe with a proxy server, since it does not protect your data against all malware.
What replaced proxy servers?
VPN. While VPNs are more secure than proxy servers, they are the best alternative to a proxy server.
VPNs come with all the benefits of a proxy server such as online anonymity and security, while they are even better in being reliable and performance stability.
Do I need a proxy server?
Having a proxy server is not urgent.
You can start using it as a server that acts as an intermediary between your device and the internet if it meets your preferences and purpose:
- Surf the internet anonymously with a hidden IP address and location.
- Improve your network performance.
- Access geo-restricted content and websites.
What happens if you don’t use a proxy server?
Since a proxy server is an intermediary between your device and the Internet, a connection without using a proxy server causes the below situations:
- Your online activity will be trackable since your IP address and location are no longer anonymous.
- You might face privacy limitations since a proxy server can enhance security.
- Your bandwidth will not be saved anymore. Proxy servers enable companies to save bandwidth and compress traffic before it reaches the user’s computer.
- You will access to geo-restricted content will be limited, and you cannot bypass the restrictions anymore.
Why is a proxy server risky?
A proxy server comes with cybersecurity risks. If you choose an untrustworthy proxy provider, you might face below situations:
- As an intermediary between a user and a web server, a proxy server can intercept your data (email, credit card, bank account) and misuse it or let hackers access it.
- A proxy server changes your IP address to not let web servers access it.
- A risky and untrustworthy proxy server can send/sell your IP address and location to the targets who care about it.
- Unlike VPNs, proxy servers do not encrypt your data and reduce security.
- You might experience broken internet following the insecure and slow proxy server.
- Because free proxies rely on ad-based income methods, which allow other parties to monitor your traffic, using them is risky.
Is A VPN faster than a proxy?
VPNs encrypt all connection requests, but proxy servers do not. So, a proxy server could be faster than a VPN.
On the other hand, free proxy servers are slow while VPNs are more secure, stable, and reliable.
What is the fastest proxy server?
There are several fast proxy servers introduced in 2024:
- hide.me Proxy
- Smartproxy
- Bright Data
- MyPrivateProxy
- Soax.io
- Oxylabs
- Brightdata
- IPRoyal
- Nimbleway
- NetNut
- Webshare
- Storm Proxies
Does proxy hide your location?
Yes. Connecting through a proxy enables you to hide your IP address and conceal your location.
In this way, your online identity and online privacy can be masked by a proxy server.
Why should I disable proxy?
According to your preferences and needs, you can disable the proxy server. However, you might face any one of the below concerns while the proxy server is enabled:
- Security issues
- Privacy concerns
- Malware redirects without your consent
- Access blocked resources and restrictions
Can I use a proxy without a VPN?
Yes. While proxies can assist in hiding your IP address, they cannot offer as much security and privacy as a VPN.
However, you can use a proxy without a VPN using below methods:
- Proxy Servers such as ProxFree.
- SOCKS Proxy which can be set up using SSH.
- Tor browser to stay anonymous.
- Web-Based Proxies.
Does a proxy server change your IP address?
Yes. Your IP address can be changed via a proxy server, which prevents the web server from knowing your precise location.
Do proxies work on mobile?
Yes. A mobile proxy is a remote proxy server that uses a mobile device’s IP address to connect users to the internet instead of their desktop or laptop computer.
Mobile proxies are used to hide the originating IP address from being seen when gaining access to content in several geographical regions.
What is an example of a proxy server?
As an intermediary between a client and a server, the proxy server is used to improve security and performance of services.
Proxy servers come in two primary varieties:
- Forward proxies
- Reverse proxies
Each proxy server can be categorized based on:
- Protocol
- anonymity level
- source
- Accessibility
How do I know if I have a VPN or proxy?
According to the device or OS you are using VPN/Proxy on, the method of checking is different. Below are ways that might be useful:
- Visit www.whatismyproxy.com to determine whether or not you are linked to a proxy.
- Look under your PC’s WiFi settings to see if a VPN or proxy is visible.
- On a Mac, check the top status bar. There should be a black box with four grey lines and one white line if you have a VPN or proxy setup.
- Navigate to the Internet Options after launching Internet Explorer. Select the Connections tab and press the bottom-mounted LAN settings button.
- Click the cogwheel icon after selecting the Start menu. The ‘Settings’ application will open. Next, choose “Network & Internet”. Select “VPN” from the sidebar on the left. Check to see if the right panel has any VPN connections.
What is the most common proxy for?
Foeward proxy. To send requests from a network to the internet through a firewall, the forward proxy is used as the most common form.
It detects which requests are rejected or allowed to pass through the firewall from the intranet.
How do I know if my proxy is safe?
To check whether you are using a safe proxy, there are some solutions:
- Use a proxy check tool to analyze if you are using a proxy or not. Consider that not all the proxies can be detected by these tools.
- Checking the type of proxy you are using. Elite and Anonymous proxies are safer than transparent proxies.
- Select reliable services to protect your sensitive data.
How much RAM does a proxy need?
2 GB is sufficient for basic proxy functionality and most purposes.
Depending on the proxy configuration, the required amount of RAM would be different:
- A minimum of 1 GB is recommended, while certain systems can require 2 GB or more.
- It is advised to have about 1 GB of memory for every TB of used storage if you are utilizing Ceph or ZFS storage.
Is A proxy server good for gaming?
Yes. Proxies offer the best gaming experience for gamers by decreasing the distance that data travels between them and the game server.
By carefully choosing a proxy server that is located closer to the game’s server, gamers can also significantly reduce latency and connection drops.
Here are some of the top gaming proxy servers:
- Proxy-Seller
- ExitLag
- IPBurger
- WTFast
- MyPrivateProxy
- Pingzapper
- NoPing
And more.
FAQ
Why do we use a Proxy server?
If you want to work with an unknown identity on the Internet and the web; a proxy server can hide your IP Address when you connect to the Internet to get what you want; It also encrypts the content of transit packets to protect your sensitive data so that third parties can not easily view the content, and also provides the ability to control and monitor the activities of other users for the organization's managers.
What are the advantages of using a proxy server?
The proxy server provides features such as increasing network security, speeding up the website, protecting users 'identities, restricting and controlling users' activity, access to blocked resources and sharing Internet connection on the LAN, which for many users It is useful and meets their needs.
Conclusion
A proxy server is used to maintain security, better use of bandwidth, monitor the performance of internal network users, and improve the speed of access to information.
Now that you know the advantages and uses of Proxy servers and their risks, you can use them properly according to your needs and desires.