Kali Linux Overview and Practical Uses
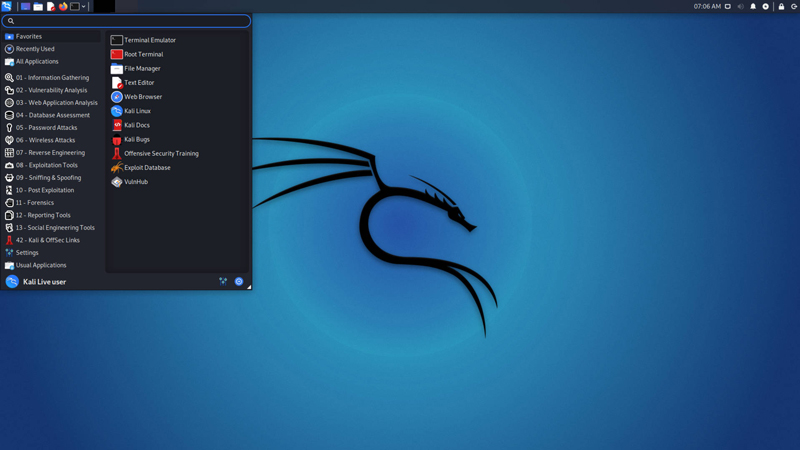
Kali Linux is a Debian-based operating system designed for penetration testing and security auditing. It offers over 600 tools essential for ethical hacking and digital forensics.
🤖AI Overview:
Kali Linux is a Debian-based OS tailored for advanced penetration testing and security auditing. It is maintained by Offensive Security and includes a wide range of tools for ethical hacking, computer forensics, and reverse engineering. Kali Linux is free and open-source, suited for cybersecurity professionals and researchers.
Why does Kali Linux get used by hackers?
While Backtrack featured several tools that all served the same goal and became overburdened, Kali Linux claims to be a more polished replacement focusing on testing instead of Backtrack’s slew of redundant utilities. Ethical hacking on Kali Linux is made easier by this.
Who developed Kali Linux?
Deavon Kearns and Mati Aharoni are the primary creators of Kali Linux. Backtrack another Linux distribution for penetration testing was reworked into this distribution. Most of Kali’s code comes from the Debian repositories. Hence its development follows the Debian guidelines. A small group of experienced developers began working on the project in the early days of March 2012. Only a few developers were authorized to commit packages in a secure environment. In 2013, the first version of Kali Linux was made available to the public. There have been a lot of significant modifications to Kali Linux since that time. Offensive Security is responsible for developing these updates.
The purpose of Kali Linux
Kali Linux is the best choice for advanced penetration testing and security auditing. Penetration Testing, Computer Forensics, and Reverse Engineering are just a few of the many information security activities that may be accomplished with Kali.
Is it illegal to use the Kali Linux operating system?
By itself, Kali Linux is not considered illegal. The OS is merely a software component. If someone utilizes it only as a means of hacking, they are breaking the law. Installing it for educational or teaching purposes, or strengthening your software or network, is allowed, as is installing any licensed and freely available operating system.
Why should we use Kali Linux?
For a variety of reasons, Kali Linux should be used. Let’s have a look at a few examples:
- Kali Linux has always been and will continue to be completely free to use.
- Kali Linux has more tools than you can imagine, with over 600 different tools for penetration testing and security analytics.
- Kali adheres to the open-source model as a Linux distribution, which is widely accepted. Their source code can be accessed through Git, making it easy to change.
- Even though most penetration tools are written in English, Kali provides real multilingual support, allowing more users to operate in their local language and locate the tools they need for the job at hand.
- Offensive security developers know that not everyone will like their design paradigm, so they’ve made it as simple as possible for the more adventurous user to customize Kali Linux to their satisfaction, right down to the kernel.
Kali Linux has several valuable tools.
There are many beneficial tools available in Kali Linux, as described earlier. The software that comes pre-installed on Kali Linux systems is listed below. Obviously, this list isn’t exhaustive and can be supplemented with more information if necessary, depending on the prerequisites and decisions of the reader.
Nmap
An open-source network scanner developed by Gordon Lyon, Nmap is known as Nmap. For the most part, it’s used to find hosts and services on a system by transmitting and analyzing packets over time. It has various features and benefits, such as identifying the operating system of a computer network.
THC Hydra
THC Hydra is one of the most effective tools available for brute-forcing a remote authentication service. For example, it can be used to launch a slew of dictionary attacks against telnet, FTP, HTTP, SMB, and other protocols. It is a multi-threaded login cracker that can attack a wide range of conventions. Like other utilities in Kali Linux, this one is fast and versatile.
Aircrack-ng
Aircrack-ng: To manipulate and attack WiFi networks, it is not just one tool but a collection of tools. NIC monitor mode is enabled as a result of this setting. The ability to capture network packets is available once it is activated. 802.11 wireless LANs are supported by a detector, packet sniffer, WEP, and WPA/WPA2-PSK cracker, and an analysis tool Monitoring mode can be enabled on any network interface controller. Its primary goal is to identify weak points in the WiFi security system. Monitoring, attacking, testing, and finally cracking are the four stages of the process.
Nessus
A proprietary vulnerability scanner created and developed by Tenable Nessus is utilized during penetration testing sessions. Use it to check your computer systems for security flaws via a remote scanning tool. It does not, however, do so on its own. Pernicious programmers may exploit these vulnerabilities to gain access to any PC affiliated with your company if it is equipped to detect them. After running more than 1200 tests and displaying alarms where security fixes are needed, it provides structures for easy cross-linking between them.
Wireshark
Protocol analyzers like Wireshark are very popular on Linux, and it’s easy to see why. It’s a packet analyzer that’s available for free and open source. If you’re searching for a way to keep tabs on the minute aspects of your network, this is the tool for you. With the help of online scanning software, you can quickly identify potential dangers, problems, and vulnerabilities on the internet. All major operating systems are supported and up to 2000 different network protocols. It’s compatible with all of Kali Linux’s standard commands.
Where to buy Kali Linux VPS Server?
It may be challenging for you to buy Kali Linux Server, as most providers do not sell Kali Linux due to illegal use. But if you need a Linux VPS with common distributions, most providers can provide you with a service.
Kali Linux’s History
Initially, the project was referred to as Whoppix or WhiteHat Knoppix. According to the name, the operating system is based on Knoppix. There were several Whoppix versions, spanning from 2.0 up to v2.7.
WHAX was born due to this (or the longhand, WhiteHat Slax). Since Slax had replaced Knoppix, the name had to be altered. A nod to the fact that it would go on from Whoppix is why WHAX started at v3.
While Auditor Security Collection (commonly shortened to just Auditor) was being developed simultaneously as BackTrack, efforts were pooled (together with WHAX) to create the latter. From version 1 through version 3, BackTrack was based on Slackware, but from version 4 onward, it was Ubuntu.
Kali Linux was created in 2013 due to all of this, following the release of BackTrack. When Kali became a rolling operating system, Debian stable was used as the engine under the hood, but Kali later switched to Debian testing.
| Date | Project Released | Base OS |
|---|---|---|
| 2004-August | Whoppix v2 | Knoppix |
| 2005-July | WHAX v3 | Slax |
| 2006-May | BackTrack v1 | Slackware Live CD 10.2.0 |
| 2007-March | BackTrack v2 | Slackware Live CD 11.0.0 |
| 2008-June | BackTrack v3 | Slackware Live CD 12.0.0 |
| 2010-January | BackTrack v4 (Pwnsauce) | Ubuntu 8.10 (Intrepid Ibex) |
| 2011-May | BackTrack v5 (Revolution) | Ubuntu 10.04 (Lucid Lynx) |
| 2013-March | Kali Linux v1 (Moto) | Debian 7 (Wheezy) |
| 2015-August | Kali Linux v2 (Sana) | Debian 8 (Jessie) |
| 16-January | Kali Linux Rolling | Debian Testing |
Conclusion
Kali Linux stands as an essential platform for anyone interested in cybersecurity, from beginners to seasoned professionals.
Its rich selection of tools, extensive community support, and continuous development make it the preferred choice for penetration testing and security auditing.
Learning to use Kali Linux can provide valuable skills for protecting networks and understanding security threats. With its open-source nature, customization options, and dedicated focus on security, Kali Linux remains a vital resource in the field of ethical hacking.
FAQ
2. Who developed Kali Linux?
Kali Linux was developed by Offensive Security, with key creators including Devon Kearns and Mati Aharoni.
3. What is the main purpose of Kali Linux?
It is used mainly for ethical hacking, penetration testing, computer forensics, and security research.
4. Is using Kali Linux legal?
Yes, it is legal to use for educational and security purposes but illegal for unauthorized hacking.
5. What are some essential tools included in Kali Linux?
Tools like Nmap, THC Hydra, Aircrack-ng, Nessus, and Wireshark are included.
6. Can beginners install Kali Linux easily?
Yes, the installation process follows Debian guidelines and is suitable for users new to security testing.
7. Does Kali Linux support multiple languages?
Yes, it offers multilingual support.
8. How often is Kali Linux updated?
It receives regular updates incorporating new tools and improvements.
9. What are the system requirements for Kali Linux?
Typically, a minimum of 2GB RAM and 20GB storage are recommended.
10. What is the history of Kali Linux?
It evolved from earlier projects like BackTrack, officially released in 2013 as a Debian-based security platform.