How to Install and Setup Fail2Ban on Your Linux Server
Install and setup Fail2Ban to protect your Linux server from unauthorized access and brute-force attacks. This guide provides step-by-step instructions for various Linux distributions.
🤖AI Overview:
Install and setup Fail2Ban to strengthen the security of your Linux server against unauthorized access and brute-force attacks. Fail2Ban acts by monitoring access attempts and blocking suspicious IP addresses temporarily with firewall rules, enhancing the server’s defense mechanism. This guide provides a step-by-step process for installing and configuring Fail2Ban on various Linux distributions to ensure server security.
Quick Steps:
1. Connect to your Linux server as a root or sudo user via SSH.
2. Update your system repository using apt-get update for Ubuntu and Debian or yum update for CentOS.
3. Install Fail2Ban with apt-get install fail2ban for Ubuntu/Debian or yum install fail2ban for CentOS.
4. Enable and start the Fail2Ban service using systemctl enable fail2ban and systemctl start fail2ban .
5. Create a local configuration file with cp /etc/fail2ban/fail2ban.conf /etc/fail2ban/fail2ban.local .
6. Edit the fail2ban.local file to customize settings like log level and bantime.
7. Setup jail.local to configure security filters and adjust parameters as needed.
8. Check the status of Fail2Ban to ensure it is active with systemctl status fail2ban .
Introduction
The risks of cyber-attacks have significantly increased with technology’s advancement, making server security crucial. Protecting data from cyber threats and preventing unauthorized access is a pressing concern for everyone active on the Internet.
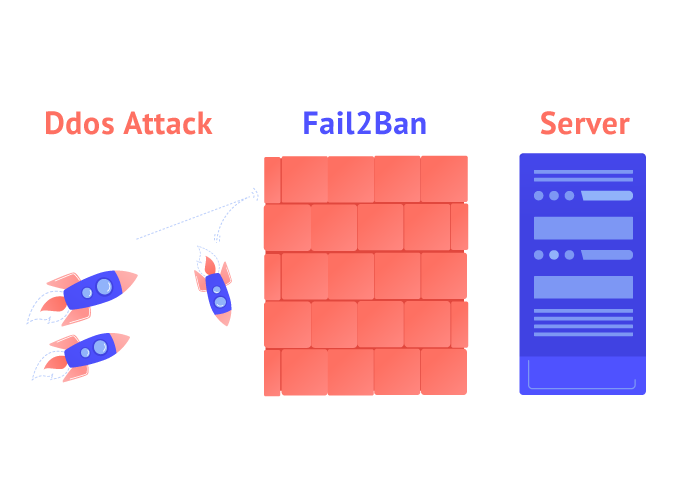
One effective tool to bolster security on Linux servers is Fail2Ban. This software enables you to block IP addresses attempting to breach your systems, particularly enhancing the security provided by a well-configured firewall. In this guide, I will explain how to install and setup Fail2Ban as a robust layer of protection for your Linux server.
Install and Setup Fail2Ban on Different Linux Distributions
Fail2Ban is part of the repository of all major Linux distributions, simplifying its installation process.
Prerequisites
Before installing Fail2Ban, ensure you have root or sudo user permissions and an up-to-date system. Connect to your server using an SSH client.
Installing Fail2Ban on Ubuntu
- Update the system repository:
apt-get update && apt-get upgradeIt is essential to have the latest system updates to ensure compatibility.
- Install Fail2Ban:
apt-get install fail2banInstall the Sendmail package for email alerts:
apt-get install sendmail - Verify the service status:
sudo systemctl status fail2banChecking the status ensures that the installation was successful and the service is active.
Installing Fail2Ban on CentOS
- Access the EPEL repository:
sudo yum install epel-release - Install Fail2Ban:
sudo yum install fail2ban - Activate and start the Fail2Ban service:
sudo systemctl enable fail2ban sudo systemctl start fail2banActivating the service ensures it runs each time the system starts.
Installing Fail2Ban on Debian
- Update the system:
apt-get update && apt-get upgrade -y - Install Fail2Ban and Sendmail:
apt-get install fail2banapt-get install sendmail-bin sendmail - Check service status:
systemctl status fail2ban
Installing Fail2Ban on Fedora
- Update the system:
dnf update - Install Fail2Ban:
dnf install fail2ban - Start and enable the service:
systemctl start fail2bansystemctl enable fail2ban
Configuring Fail2Ban
Fail2Ban configuration involves editing two files: fail2ban.local and jail.local
Editing Default Settings
- Create a local copy of the configuration file:
cp /etc/fail2ban/fail2ban.conf /etc/fail2ban/fail2ban.local - Modify settings with a text editor:
sudo nano /etc/fail2ban/fail2ban.local
Key Configuration Parameters
- Log Level (loglevel): Determines the severity of the log messages. Using “INFO” helps track regular activities.
- Bantime: Specifies the duration an IP is banned. Adjusting this interval can balance between security and user inconvenience.
- Maxretry: Sets the number of invalid login attempts permitted before a ban.
- Ignore IP: Allows you to whitelist trusted IP addresses to prevent them from being unintentionally blocked.
Creating backup copies of configuration files is recommended to preserve custom settings and avoid overwriting them during updates.
Fail2Ban Report Levels
The report you receive has different levels, which we will explain below:
CRITICAL: This is an emergency situation that requires immediate attention.
ERROR: Displays a problem that is not as important as CRITICAL.
WARNING: Conditions that may be dangerous.
NOTICE: A common but important condition.
INFO: You can skip INFO messages.
DEBUG: These are debug-level messages.
FAQ
2. How do I install Fail2Ban on Ubuntu?
To install Fail2Ban on Ubuntu, update your repository with apt-get update and then use apt-get install fail2ban to install the software.
3. What are the main configuration files for Fail2Ban?
The main configuration files are fail2ban.conf for operational settings and jail.conf for custom security rules and filters.
4. How do I start the Fail2Ban service?
After installing Fail2Ban, start the service using the command systemctl start fail2ban and enable it to run on boot with systemctl enable fail2ban .
5. Why is it important to create a local configuration file for Fail2Ban?
Creating a local configuration file like fail2ban.local preserves custom settings from being overwritten during software updates.
6. Can Fail2Ban be used alongside a firewall?
Yes, Fail2Ban complements a firewall by adding additional layers of security, helping to block IPs attempting unauthorized access.
7. What settings can I adjust in the jail.local file?
In the jail.local file, you can adjust settings such as bantime, maxretry, and configure filters for various services to protect your server.
8. How do I verify that Fail2Ban is running?
You can verify that Fail2Ban is running by using the command systemctl status fail2ban to check its status.
9. What is the purpose of the bantime setting in Fail2Ban?
The bantime setting determines how long a malicious IP address will be blocked from accessing the server after exceeding the maximum number of login attempts.
10. How often should I update Fail2Ban?
It is recommended to update Fail2Ban regularly to ensure you have the latest security patches and features to protect your server effectively.
Conclusion
Fail2Ban is a crucial tool for safeguarding your Linux server against brute-force attacks. By monitoring logs for suspicious IP activity and taking appropriate action, it acts as a first line of defense. Follow this guide to install and configure Fail2Ban on various Linux distributions and enhance your server’s security. For any questions, feel free to engage in the comments section.