Remote Host Identification Has Changed in Windows & Linux
If you prefer to have remote access to a computer without using GUI, you certainly work with SSH. Users and developers use the SSH as a shell-based remote access protocol to connect to another machine. Remote Host Identification Has Changed is one of the potential errors that safeguards the connection of users against specific harmful attacks. Windows, Linux, and macOS users might face while using SSH. It is one of the safest methods for connecting to a web server. You can securely access an unsecured network with this command-line tool. Since this error concerns users about security, users try to find a solution to have a secure connection.
If you feel someone is eavesdropping on your server, this guide is just what you need. Join us with this article and review different methods that enable you to solve this issue on your considered operating system after buy VPS. Before that, we explain some essential definitions to freshen your memory or close you to the basic required knowledge to fix the Remote Host Identification Has Changed warning.
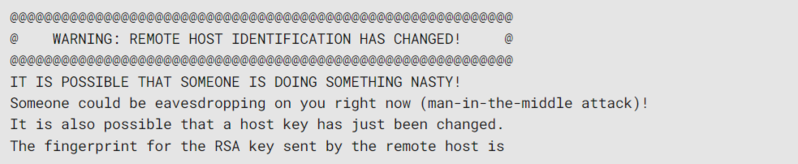
When you attempt to connect to a remote host via SSH, the ‘Warning: Remote Host Identification Has Changed’ error occurs. The host’s key has changed since you last connected. This can happen if the host has been reinstalled, upgraded, or compromised by an attacker. There is a possibility of a man-in-the-middle attack where someone intercepts your connection and pretends to be the host.
A host identification mechanism for use on Internet Protocol (IP) networks, such as the Internet, is the Host Identity Protocol (HIP). IP addresses and the Domain Name System are the two primary namespaces on the Internet. Your Secure Shell (SSH) keys and the server “fingerprint” a client will look for are both involved in the problem. Secure Shell will prevent access to your server and send an error if it detects a problem.
However, before any action to solve the Remote Host Identification Has Changed error in Windows, Linux, and Mac, you must check whether the error is caused by an actual threat and distinguish between a genuine MITMA and a false alarm. To do this, verify the below considerations:
- You recently changed your SSH private key or passphrase.
- A new server has been set up for you.
- One IP address was assigned to several distant systems.
- You shut down your server and then launched a new one using the old IP.
- Alternately, reinstall your OS.
You can be more certain that the error is a false positive and that there are no hazards if any of these apply to your situation. Of course, you might have completed one or more of these tasks and forgotten about them when you later tried to get back into the VPS. If you share a virtual private server with someone else, that person might have made these changes without your knowledge. We advise you to quickly review the logs of whichever SSH client you are using if you have any questions. This log page typically lists all recent significant server modifications with their timestamps in full.
Understanding SSH
SSH, commonly referred to as Secure Shell or Secure Socket Shell is a network protocol that allows users, in particular system administrators, to securely log in to another machine on an insecure network. Public keys for authentication and strong passwords are supported by Secure Shell, which transmits encrypted data between two devices when linked over a network like the Internet. Network administrators frequently use SSH to remotely administer systems and software. SSH enables them to get into a different computer over a specific network, issue commands, and move data between devices. As a result, SSH can refer to both the network protocol and the collection of tools that make it function.
The server-client model is used by SSH. It links a server running the session to an SSH application that displays the session. SSH implementations frequently include support for various application protocols, which are employed for sharing files and simulating terminals. Standard TCP port 22 serves as the SSH protocol’s default port. If you use the default SSH port number, hackers can simply access the data you transfer. To avoid a brute-force assault, adjust the default SSH port number if you require an extremely secure connection.
What is the Concept of SSH Remote Host Identification
Getting the error notice remote host identification has changed indicates that the key stored for the host you’re trying to connect to has changed. There are many various reasons why this could occur, however connecting to a different server than the one you were first connected to is frequently to blame (for instance, your server might have been rebuilt by a new one). The public key of every server we connect to via SSH is kept in our home directory. known_hosts is the name of the file. When you re-connect to the same server, SSH will check that the public key in use matches the one you have saved in our known_hosts file. This issue means that the server’s key has changed since the last time we connected to it.
An attacker will insert a fake SSH server with the same IP address between your connection and your server during a Man-in-the-Middle attack (MITMA). The network traffic will subsequently be redirected to the actual SSH server. This will allow the attack to go undetected and prevent you from discovering their surveillance operation. Your SSH software will presume that a malicious online attack is unlikely to protect against such an occurrence. The server will notice that the unique certificate doesn’t match if a hacker snoops on your connection and intercepts it.
Why Remote Host Identification Has Changed Occurs in Windows & Linux
When using SSH to connect to a remote server, and the server’s key has changed since you last connected to it, you frequently get the Remote Host Identification Has Changed error message in Windows and linux. Several factors, including reinstalling the server or changing the server’s IP address, could cause this.
The Warning: remote host identification has changed problem typically appears when the server’s unique fingerprint does not match the information saved in the known_hosts file. Whenever you modify your password or rebuild your VPS host, this key regularly changes. Your SSH program will notice a change in your connection when these changes are done and report a security error. This is beneficial because it enables you to determine whether a hacker is attempting to attack you, such as with a man-in-the-middle assault.
Solutions to Fix Remote Host Identification Has Changed in Windows
As the first solution, we will explain the Warning: Remote Host Identification Has Changed issue repair for Windows. As long as you have the proper login information, you may access your website from practically wherever you can access the internet. In addition, an SSH client is typically included with the OS on Linux and macOS computers. On Windows, a special interface is required.
The problem has different remedies depending on whether you are using an SSH client for Windows like PuTTY or the built-in SSH terminal in Windows to run your SSH connection. Let’s first discuss the first approach, which addresses both the Windows SSH terminal and some SSH clients like the OpenSSH client. After that, as PuTTY is the most widely used and well-known SSH client worldwide, we’ll discuss how to solve the problem in PuTTY.
Method 1. Windows PowerShell
This fix functions with the default Windows SSH Terminal and some SSH clients, but not all of them. Follow the below-required steps to fix the issue using this solution:
- To access your user folder, press the Windows key + R. Once it is opened, run the command below:
%USERPROFILE%- In the “.ssh” folder, find the “known_hosts” file and open it with Notepad.
- A list of keys that your SSH protocol uses to create remote access connections can be found inside the “known_hosts” file that you just opened in Notepad. Use the error code to find the faulty key, then delete it. After saving the changes and closing Notepad, your work is complete.
Method 2. PuTTY
PuTTY is a popular SSH client that many people favor. If you are one of them and face Remote Host Identification Has Changed error in puTTY, the answer is somewhat different. However, the overall answer is still the same. The keys are kept somewhere else. To identify the problematic key, follow the paths below:
- First, you must open the Windows registry. To do this, you can hold the Windows key + R and run the following command:
regeditAlso, you can open the Windows registry by clicking on the Windows symbol in the bottom left corner, perform a search for “regedit,” and then launch the application.
- The second step of this method asks you to Find the key in the Windows registry. To do this, look for the below directory in the top search bar:
hkey_current_user/Software/SimonTatham/PuTTY/SshHostKeys/
You will see a list of keys used by your PuTTY SSH client to create a remote access connection here once more. Find the faulty key and refer to the error code once more. Simply delete the given key by using the right-click menu.
Solutions to Fix Remote Host Identification Has Changed in Linux
Linux users who are pursuing this guide may have skipped the previous section to find the answer they’re looking for. Sure! This part is all yours with three different methods to fix the Remote Host Identification Has Changed error.
With all of its benefits, using SSH key on Linux for authentication reduces a lot of dangers and weaknesses. This solution works for all Linux distributions. On your Ubuntu, Debian, or CentOS system, you just need to open up the Terminal to run the related commands of each method.
Method 1. Use SSH-Keygen Commands
To use this method, follow the below path to use the SSH-Keygen and solve the warning:
- Once your terminal is brought up, type the following three commands in it one at a time, press enter after each one to execute them:
Ssh-keygen -R hostnamessh-keygen -R ipaddressssh-keygen -f “~/.ssh/known_hosts” -R “VPS_IP”This will delete any keys that might be the problem and update the “known_hosts” File.
Method 2. Remove the Old Key
To solve the Remote Host Identification Has Changed error using this method, open the “known_hosts” file using a text editor of your choice (such as nano), fix the broken key, and then close the file. The below steps show you the solution in detail:
- Open any text editor you may have available and use the Terminal to locate the “known_hosts” folder. You can find your folder by using the error itself as a guide. The folder will ordinarily be located in the following directory:
~/.ssh/known_hosts.- Now, edit the “known_hosts” File:
nano ~/.ssh/known_hostsLocate the line containing the fingerprint of that VPS. Typically, you can locate it on the error line, remove it, save your work, and then quit nano. Your issue should be resolved, therefore you can now close the editor.
Method 3. Use SSH stricthostkeychecking Options
To use this way and fix Remote Host Identification Has Changed in Linux, you just need to run the following command to remove the old host key in the “known_hosts” File and replace it with a newly generated key.
- Open the terminal, type the following command and press Enter:
ssh <device IP address> -o stricthostkeychecking=noIn this way, you should have no problems anymore. However, interested users can find out more ways to keep Secure SSH Server in Linux.
Solutions to Fix Remote Host Identification Has Changed in macOS
The Terminal or a paid app like SSH Config Editor can be used to repair the problem on a Mac. We advise you to choose the choice that best suits your needs because the results will be the same. Our preferred approach is to first open the file in a Terminal window before opening it in one of several specialized editors, such as Nano or Vim. This is due to the fact that it is easy to use and available to all users, regardless of skill level. The error message Remote Host Identification Has Changed will be eliminated.
Method 1. Using Nano
This method uses Nano to access the Terminal and remove the faulty key. To use this method, follow the below path:
- Open your Terminal.
- To delete the key, run the command below to access the “known_hosts” File:
nano ~/.ssh/known_hostsBy doing this, a new Nano page will open, displaying all the keys included in the “known_hosts” file. Once more, use the error code to locate the problematic key, then just delete it.
Method 2. Use MAC Terminal
If you want to change the “known_hosts” file without using an editor like Nano, there is a more straightforward method. Just follow the below steps:
- Open a Terminal tab and run the command below followed by your website or host name.
ssh-keygen -R www.operavps.comIt’s crucial that you manually locate the problematic key and take it out of the Terminal. You won’t be prompted, and if you move forward without providing any information, all the keys will be lost. So take care. After deleting these keys, you must no longer see the Remote Host Identification Has Changed error.
Conclusion
In this article, you learned How to Fix Remote Host Identification Has Changed error in Windows, Linux, and Mac. Now, you know about SSH, its role in causing this error, and why the error displays generally. It’s important to remember that the error message might be trying to warn you about real problems. As a result, it is urged to avoid dismissing it as a minor oversight that should be overlooked. In this situation, the likelihood of an internet incursion is very high, so you should ensure that MITMA is not being used against you.
Both the service provider and the customer will suffer if the SSH connection’s key is somehow hacked. Therefore, it is imperative to address the Warning: Remote Host Identification Has Changed error as soon as you can.
If you follow the solution steps of your preferred operating system, you can smoothly solve the Remote Host Identification Has Changed error warning but do not hesitate to contact us if you encounter any problems. Our technical support team will try their best to solve your problems.